ӨМІР СҮР, ҮЙРЕН,
ІСКЕ АСЫР
УНИВЕРСИТЕТ
ЖАҢАЛЫҚТАРЫ
УНИВЕРСИТЕТ
ЖАҢАЛЫҚТАРЫ
03.08.2023
Әл-Фараби атындағы ҚазҰУ ғалымдары 75 ғылыми жобаны ұтты
Қазақстан Республикасы Ғылым және жоғары білім министрлігінің 2023-2025 жылдарға арналған ғылыми жән..
31.07.2023
Жазғы универсиадада спортшымыз жеңіс тұғырынан көрінді
Қытайда өткен 31-ші Дүниежүзілік жазғы универсиадада Сәдуақас Бекарыс 100 келі салмақ дәрежесінде д..
31.07.2023
ҚазҰУ студенті Дүниежүзілік универсиадада тағы бір медаль жеңіп алды
Әл-Фараби атындағы Қазақ ұлттық университетінің студенті Константин Малиновский Дүниежүзілік универс..
Анонс
БАРЛЫҚ АНОНСТАР
18.10.2023
03.08.2023
31.07.2023
31.07.2023
30.07.2023
30.07.2023
29.07.2023
ЖЫЛДАМ СІЛТЕМЕЛЕР
Студенттерге
Ректордың виртуалды қабылдау бөлмесі
Факультеттер
Cтуденттерге қызмет көрсету орталығы
'Қазақ университеті' Баспа үйі
Кітапхана
Кампус
Жемқорлықтан тыс университет жобасы
ҚазҰУ хабаршысы
Репозиториялар
Интернет кітап -дүкені
"Қазақ университеті" газеті
Green Bridge
Мемлекеттік сатып алу
Серіктестердің картасы
Кәсіподақ комитеті
Спорт
Виртуалды тур
Стратегиялық зерттеулерді дамыту Халықаралық орталығы
Этика мәселесіне қатысты өкілетті тұлға
AL-Farabi Business school
ҚАЗҰУ
БІЛІМ БЕРУ

Әл-Фараби атындағы ҚазҰУ-дің бакалавриат, магистратура, PhD докторантура бойынша 2017-2018 оқу жылына арналған мамандықтар тізімі
Шанхай ынтымақтастық ұйымының желілік университеті
Университет ШЫҰ-ға мүше мемлекеттердегі бұрыннан бар университеттердің, сондай-ақ байқаушы елдер мен диалог бойынша серіктес елдердің мемлекетаралық желісі болып табылады.

MBA бағдарламасы - бұл басқарушылық біліктіліктер спектрін кеңейтіп, тәжірибесін жүйелеу, корпоративті менеджмент, қаржы, маркетинг, персоналды басқару, бизнестің экономикалық және құқықтық аспектілері, халықаралық экономика салаларындағы жаңа тәжірибелік білім мен жаңашыл пайдалы идеялар; мансап, бизнес және жеке өсуді дамытудағы қуатты импульс.

әл-Фараби атындағы ҚазҰУ-де қашықтықтан білім беру технологиялары (ҚБТ) екінші жоғары (оқу мерзімі 2 жыл) және қысқартылған білім беру (оқу мерзімі 3 жыл) бағдарламалары бойынша сырттай бөлімдегі студенттерге, академиялық мобилдiлiк бағдарламалары бойынша шет елдік іс сапарға шыққан- 2-4 курс бакалавриат және магистартура студенттеріне, онымен қатар мүмкіндігі шектелген студенттерге пайдаланылады.

Ғылым және білім интеграциясы жобасы РМК «Ғылым ордасы» базасында ҚР БҒМ ҒК ҒЗИ мен әл-Фараби атындағы ҚазҰУ-нің магистранттар мен PhD докторанттарын дайындау бойынша бірлескен оқу бағдарламасының негізінде іске асырылады.
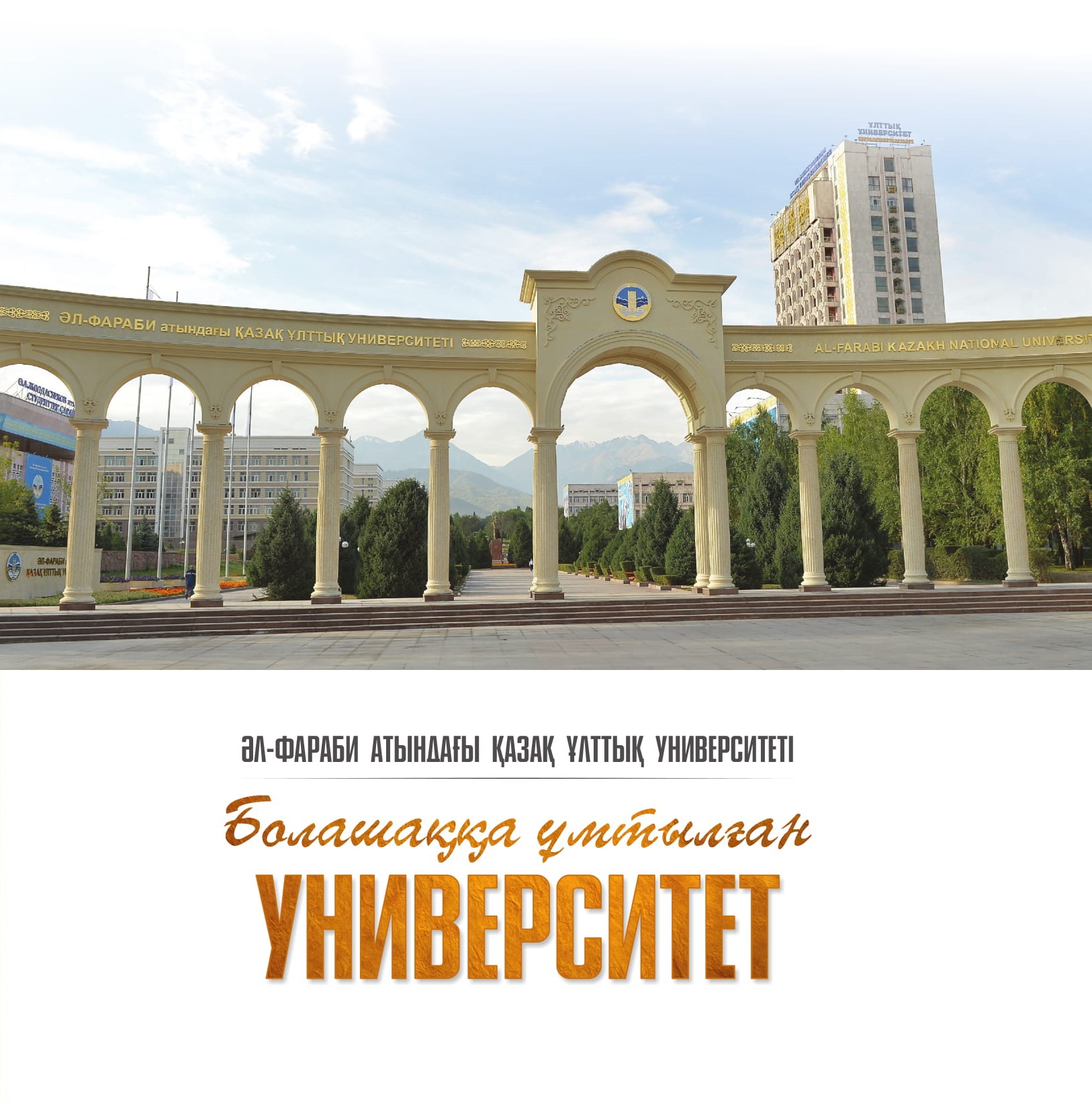
УНИВЕРСИТЕТ ТУРАЛЫ
-
ғылым және зерттеу
Студенттік өмір
инфрақұрылым
кәсіподақ және серіктестер